Image by mcmurryjulie from Pixabay
Do you know that 88% of online shoppers trust online reviews that same way they rely on personal recommendations? Moreover, 90% of consumers would read online reviews before making a buying decision. That is why Google Reviews is essential to the success of your business; it helps convert business prospects to customers. And most importantly, reviews are now an integral factor in the Google Search Algorithm.
Search engines use online reviews to rank websites for local searches. Although reviews are not the only factor that enhances ranking, it does pull a lot of weight. So, if you want your business to gain visibility in the search engines, you should take Google Reviews seriously.
How do you rack up enough reviews to impress the search engine giants? Well, there are no magic buttons here. It requires a systematic approach; you need to be proactive and focus on inspiring your customers to post great reviews for your business.
Follow these tips below to help build impressive Google Reviews.
Focus on Excellent Customer Experience. Your customers must be delighted with your service to be inspired to leave positive reviews for your business. So, make sure you deliver a service that would earn you the great reviews that you want. In summary, the delivery of outstanding customer service would bring five-star reviews to your business naturally.
Solicit for Google Reviews Directly. One of the best methods to get a review is to ask the customers directly. However, make sure the customer is absolutely satisfied with your service. When you are having a conversation with a contented customer, simply ask such a customer to write a review, and you’ll likely get a great one.
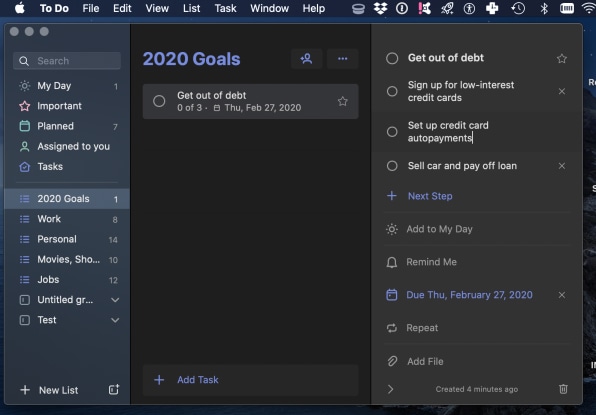
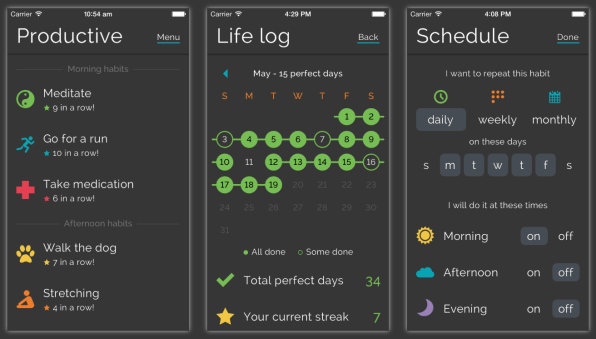
Use Innovative Ways to Solicit Reviews. A recent Local Customer Review Survey shows that seven out of ten customers will write a review when you solicit directly. Only a few will take the initiative to leave a business review without you asking, while the rest would not. That is why it is essential to make it a habit to request reviews. However, you have to be innovative with your approach.
For instance, you can request a Google Review during a business transaction. In your email, thank the customer for his/her patronage. Let the customer know the importance of feedback to your business. After that, tell the customer you’ll appreciate a review and leave a link to your business on Google Reviews.
Follow Up on Your Request for Reviews. Not all customers will leave a review the first time you asked. The fellow might be busy or may have forgotten. So, it will be smart to send a reminder to such customers using a follow-up email template.
It is crucial not to sound too pushy. So, limit the follow-up request to a maximum of three. You can send messages to the customer every week or fortnightly. Once you hit your max with a customer, stop sending such messages. Let’s be practical, some people will never leave a review no matter how many times you ask. However, maintaining consistent contact with your customers will keep your business fresh in the customer’s mind and increase loyalty.
Give Out “Leave Us a Review” Cards. You can make a special card that has a shortened link to your Google Review page. This approach is common with local contractors and service companies, but you can adapt it to your business as well. If you do not fancy printing cards, you can choose to use a digital version of the card. You can outsource the design on any freelance site or take a DIY route by using tools such as Canva. Make sure the card is branded for your business to make it look professional.
Respond to Reviews. It is good practice to respond to reviews, whether it’s a positive one or negative. This article on strategies for responding to negative reviews teaches you genuine and sustainable ways of building your online reputation.
Here is a brief outline for responding to negative reviews.
- Address the issue raised.
- Tender an unreserved apology, even if it’s not your company’s fault.
- Do your best to resolve the issue privately.
This Google Publication proves that Google acknowledges companies that respond to reviews.
Add Google Review Link to your Customer Surveys. The feedback from customers is an essential tool for improving your services. That is why it is essential to send out a survey poll to your customers occasionally. Adding a link to your business on Google Review is an excellent addition to your customer survey routine. You’ll likely have a high positive response.
Do You Need A Little Help with Reviews?
The procedure of creating a steady flow of great reviews for your business is easier said than done. An easier approach is to allow professionals to handle all the hassles of review generation while you focus on providing excellent services.
Get in touch to learn about our digital services that create a steady pipeline of leads and sales for your business.
or call us (888) 766-3315